- Report: #630167
Complaint Review: O & J Enterprises ins. dba Bulldog construstion & handyman work - Woodland Hills California
O & J Enterprises ins. dba Bulldog construstion & handyman work O & J Enterprises inc. DBA Milano Design Shoddy workmanship and Mr. Halifi is not a Licensed Contrator Woodland Hills, California
Do no be fooled by the new Company Name, this is the same company I filled a previous rip-off report under the name of O & J Enterprises Inc. DBA Milano Design, see report. We have been in a long hard battle with Mr. Halifi and the California State License board to get 16,000.00 worth of poor workmanship issues corrected including an unsafe fireplace which Mr. Halifi cares nothing about. The mere fact that He could have no reguard for our personal safety is outragious!!! This license is in the name of a Corporation, not an individual. Mr. Halifi is not a Licensed contractor, never took the California State Exam which can be verified by the License Board. He must have a RMO (Responsible Managing Officer) who is a licensed contracter to conduct business. The problem with this is that the RMO who should be in constant contact with Mr. Halif and oversee every remodel job does not. He just sits back and collects his monthly fee for being on the License. At the time of our remodel, Brett Garrett was the RMO on the License and knew nothing before during of after our remodel was complete. When after filling a complaint with the License Board I then found out what the roll of the RMO is and decided to contact Mr. Garrett. When I did speak with him and told him of our poor workmanship problems,he stated that he knew nothing about if and would contact Mr. Halifi and get back to me. He was simpathatic with us in the beginning but quickly realized that this job would also effect him and his other license and would not speak to us anymore. In addition within a week he removed himself as RMO from Mr. Halifi License which speaks volumes. Within two weeks Mr. Halifi had another RMO added to his license, Mr. Gilliland Dana Allen.
Now after almost a year we finally have an abritration date, September 2, 2010. This arbitration date could have been alot sooner but Mr. Halifi told the Arbitration Board that he would be out of the county all summer. We had a couple of friend try to contact him for work just to see if he truly was out of the county and guess what, he lied just to prolong our agony and hope he could fustrate us so much that we would drop this case. That will never happen!!!
Why the California State License board allows LIcenses to be set up this way is completly deceptive to the consumer. Mr. Halifi should not be able to present himself as a Licensed Contracter unless he has taken the State Board exam period!!! This hiding under the Corporation name is and should be against the law. I have filled a huge complaint to the Department of Consumer Affairs addressing this very issue.
In closing I would just like to say again, don't be fooled by the new name, see my other report under O & J Enterprises Inc. DBA Milano Design. Oh I almost forgot to tell you that Mr. Halifi not only changed the name of his company, he also dropped his Workmans Comp Insurance which mean if he is out there somewhere doing construction work and has workers doing on the job, that is against the law. And knowing that Mr. Halif does none of the work himself or inspects the work leads me to believe that he is not operatiing under the guidelines of the California State License Board. Please do not let this happen to you, this is the most stressful and agonizing situation we have ever been though, thank god we have a strong marrage or something like this could tear a marrage apart.
1 Updates & Rebuttals
ben halifi
calabasas,California,
United States of America
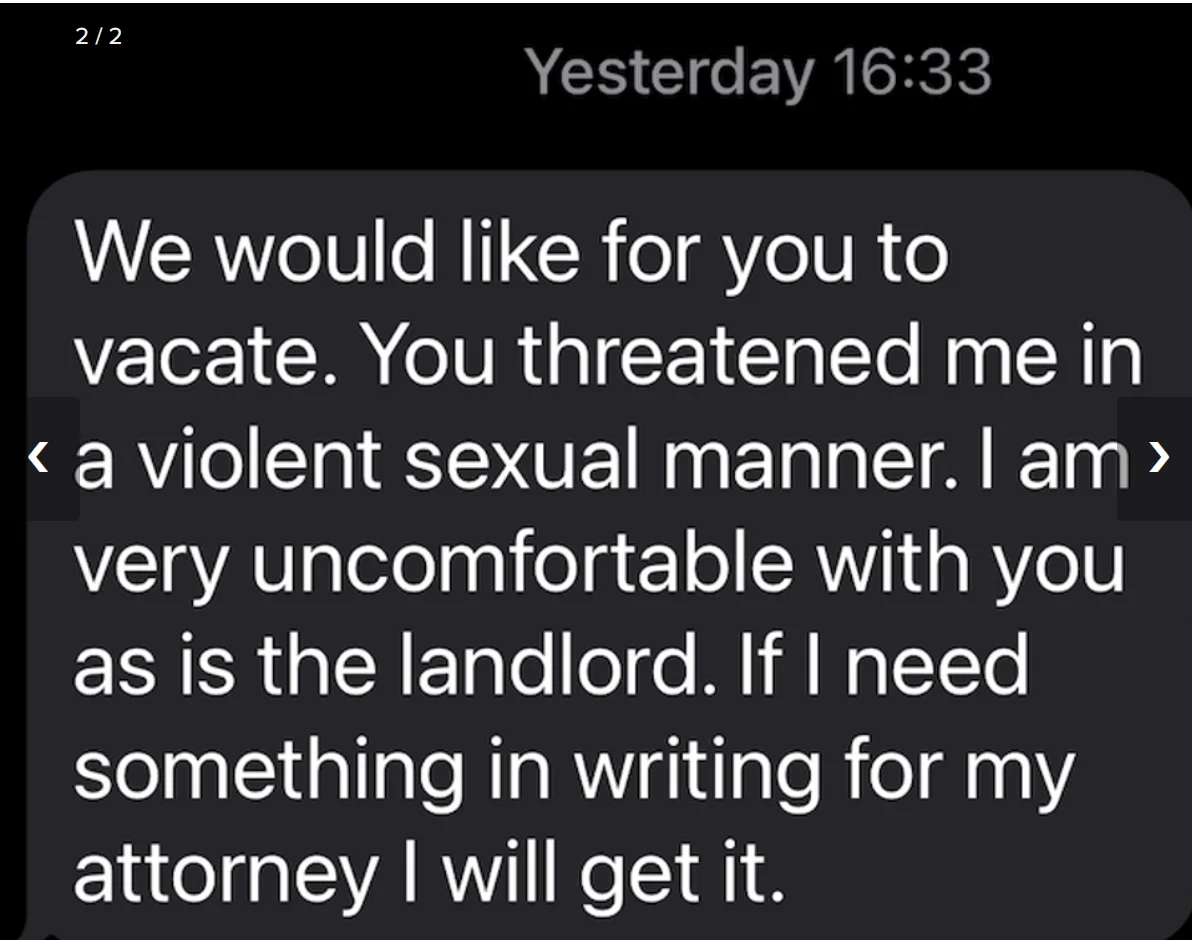
great cyber stalking
#2REBUTTAL Owner of company
Mon, November 22, 2010
A number of key factors have been identified:
- False accusations. Many cyberstalkers try to damage the reputation of their victim and turn other people against them. They post false information about them on websites. They may set up their own websites, blogs or user pages for this purpose. They post allegations about the victim to newsgroups,
chat rooms or other sites that allow public contributions, such as Wikipedia or Amazon.com.[4] - Attempts to gather information about the victim. Cyberstalkers may approach their victim's friends, family and work colleagues to obtain personal information. They may advertise for information
on the Internet , or hire a private detective. They often will monitor the victim's online activities and attempt to trace their IP address in an effort to gather more information about their victims. [5] - Encouraging others to harass the victim. Many cyberstalkers try to involve third parties in the harassment. They may claim the victim has harmed the stalker or his/her family in some way, or may post the victim's name and telephone number in order to encourage others to join the pursuit.
- False victimization. The cyberstalker will claim that the victim is harassing him/her. Bocij writes that this phenomenon has been noted in a number of well-known cases.
- Attacks on data and equipment. They may try to damage the victim's computer by sending viruses.
- Ordering goods and services. They order items or subscribe to magazines in the victim's name. These often involve subscriptions to pornography or ordering sex toys then having them delivered to the victim's workplace.
- Arranging to meet. Young people face a particularly high risk of having cyberstalkers try to set up meetings between them.[6]
[edit] Behaviors
Cyberstalkers meet or target their victims by using search engines, online forums, bulletin and discussion boards, chat rooms, and more recently, through online communities such as MySpace, Facebook, Bebo, Friendster, Twitter, and Indymedia, a media outlet known for
More commonly they will post defamatory or derogatory statements about their stalking target on web pages, message boards and in guest books designed to get a reaction or response from their victim, thereby initiating contact. [7] In some cases, they have been known to create fake blogs in the name of the victim containing defamatory or pornographic content.
When prosecuted, many stalkers have unsuccessfully attempted to justify their behavior based on their use of public forums, as opposed to direct contact. Once they get a reaction from the victim, they will typically attempt to track or follow the victim's internet activity. Classic cyberstalking behavior includes the tracing of the victim's IP address in an attempt to verify their home or place of employment. [7]
Some cyberstalking situations do evolve into physical stalking, and a victim may experience abusive and excessive phone calls, vandalism, threatening or obscene mail, trespassing, and physical assault.[7] Moreover, many physical stalkers will use cyberstalking as another method of harassing their victims.[9][10]
A 2007 study, led by Paige Padgett from the University of Texas Health Science Center, found that there was a false degree of safety assumed by women looking for love online.[11][12]
[edit] Cyberstalking legislation
[edit] United States
The current US Federal Anti-Cyber-Stalking law is found at 47 USC sec. 223.[13]
The first U.S. cyberstalking law went into effect in 1999 in California. Other states include prohibition against cyberstalking in their harassment or stalking legislation. In Florida, HB 479 was introduced in 2003 to ban cyberstalking. This was signed into law on October 2003. [14]
Some states in the U.S. have begun to address the issue of cyberstalking:
- Alabama, Arizona, Connecticut, Hawaii, Illinois, New Hampshire, and New York have included prohibitions against harassing electronic, computer or e-mail communications in their harassment legislation.
- Alaska, Florida, Oklahoma, Wyoming, and California, have incorporated electronically communicated statements as conduct constituting stalking in their anti-stalking laws.
- Texas enacted the Stalking by Electronic Communications Act, 2001.
- Missouri revised its state harassment statutes to include stalking and harassment by telephone and electronic communications (as well as cyber-bullying) after the Megan Meier suicide case of 2006.[15]
- A few states have both stalking and harassment statutes that criminalize threatening and unwanted electronic communications.
- Other states have laws other than harassment or anti-stalking statutes that prohibit misuse of computer communications and e-mail, while others have passed laws containing broad language that can be interpreted to include cyberstalking behaviors
Cyberstalking has also been addressed in recent U.S. federal law. For example, the Violence Against Women Act, passed in 2000, made cyberstalking a part of the federal interstate stalking statute. Still, there remains a lack of legislation at the federal level to specifically address cyberstalking, leaving the majority of legislative prohibitions against cyberstalking at the state level.[7]
Most stalking laws require that the perpetrator make a credible threat of violence against the victim; others include threats against the victim's immediate family; and still others require the alleged stalker's course of conduct constitute an implied threat. While some conduct involving annoying or menacing behavior might fall short of illegal stalking, such behavior may be a prelude to stalking and violence and should be treated seriously.[16]
Online identity stealth blurs the line on infringement of the rights of would-be victims to identify their perpetrators. There is a debate on how internet use can be traced without infringing on protected civil liberties.